Measuring Data Center Security
A Framework for Evaluating Campus, Facility, and Near-Asset Resilience
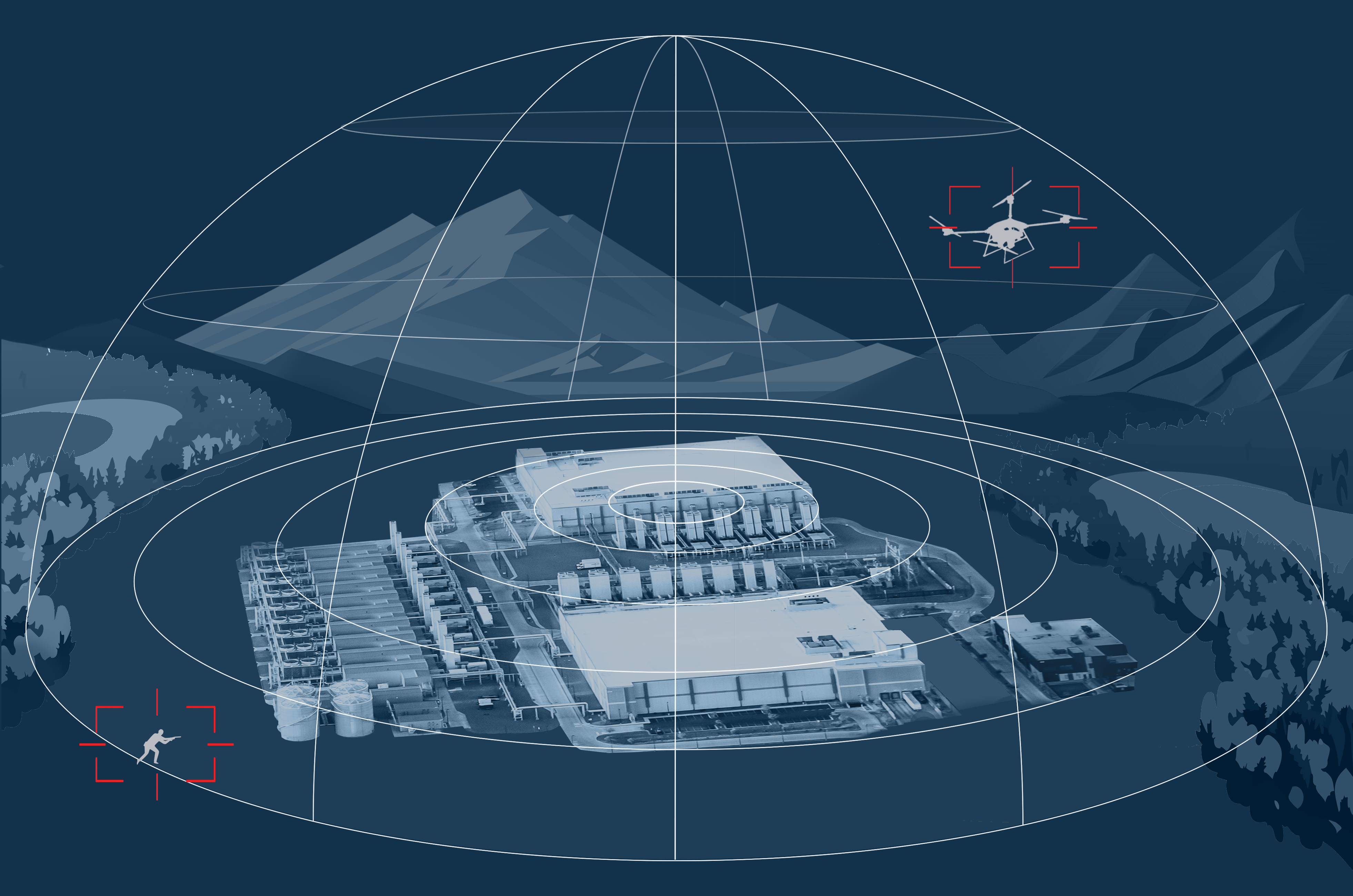
Architecture
Security Is Determined by How Defense Is Structured
Data center security effectiveness depends on how layers are placed, how access and approach vectors are covered, and how failure modes are addressed as threats move closer to critical systems and operations.
Architecture is more than the disparate placement of security devices. It defines whether the campus perimeter, building envelope (include low altitude airspace), interior pathways, and operational zones are actually defended. Even devices in a layered configuration are limited to direct functionality if the greater architecture is not designed and implemented as a whole.
Security architecture is what creates defensible positions.
Methodology
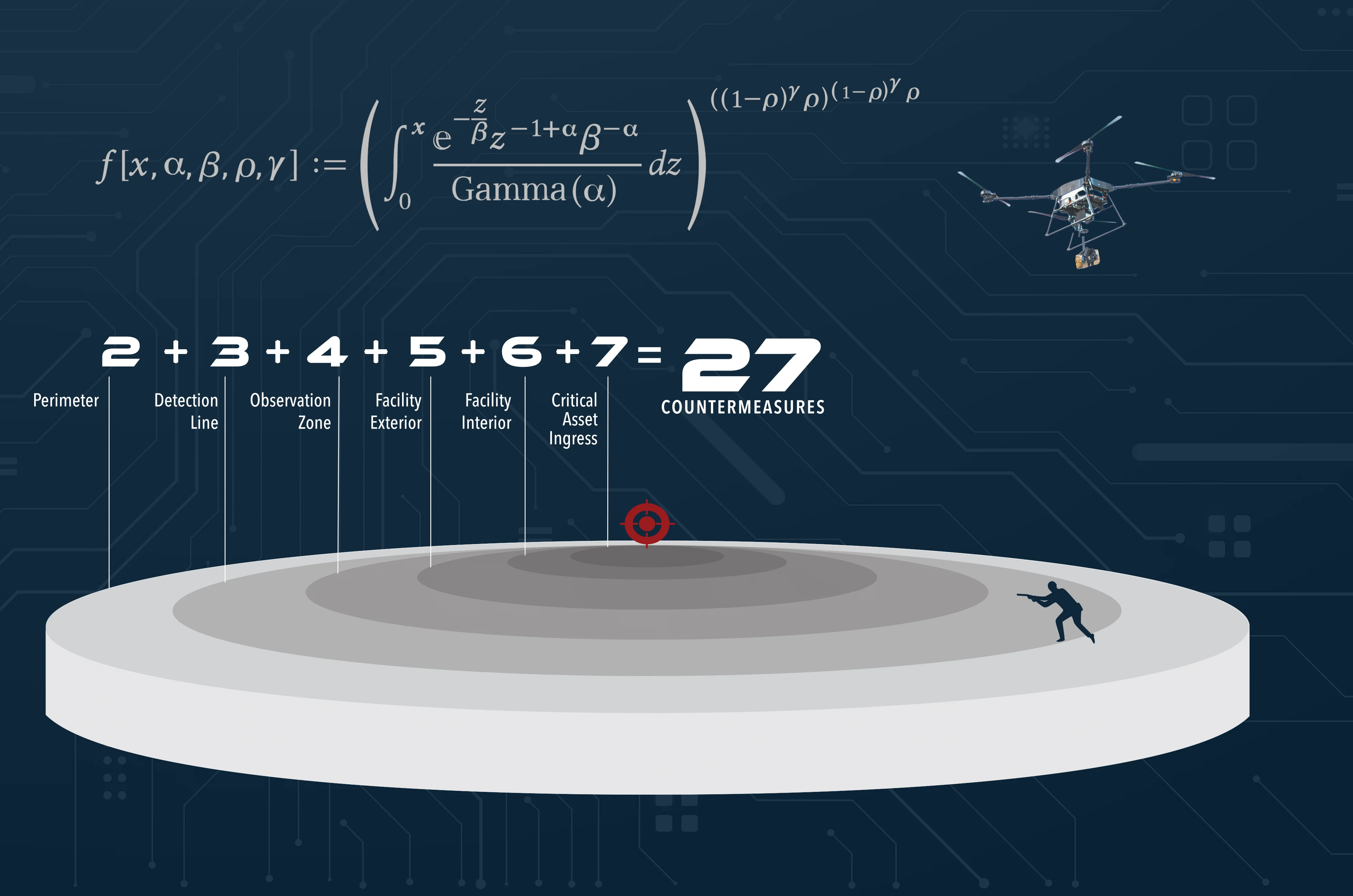
Defense Maturity Is Cumulative Across Ordered Layers
Effective protection is achieved through sequential layers of defense, each increasing the difficulty of compromise along defined paths to critical systems, operations, and continuity.
In order to build resilience, each ordinal layer must increase in both quantity and quality of countermeasures so that a single failure does not become a single point of loss. This cumulative approach guards against known failure modes in complex operating environments, including airspace threats.
This is the foundation of Cumulative Defense Strategy.
Measurement
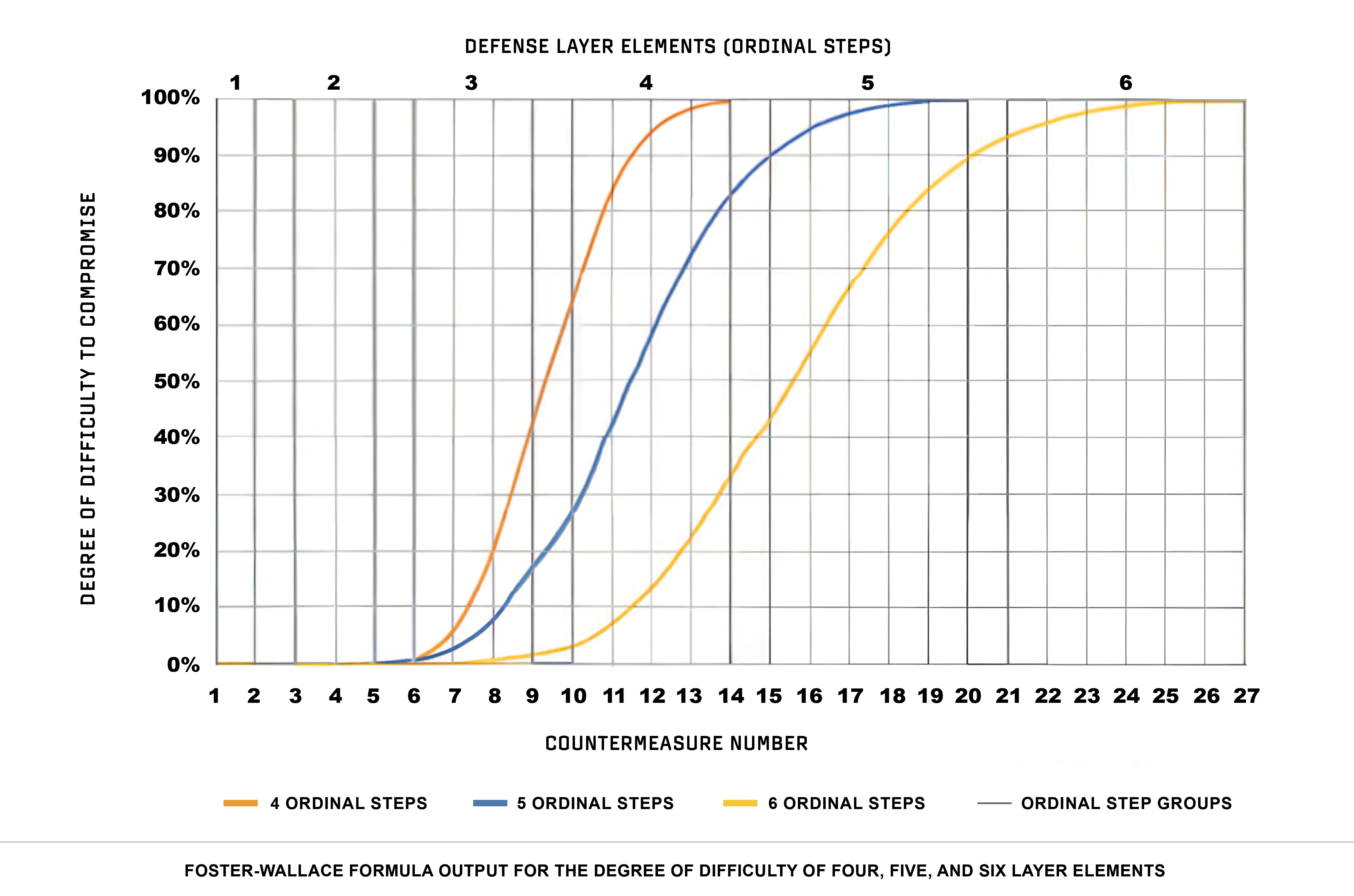
Mathematical and Objective Consistency
If defensive difficulty does not increase as threats move closer to critical systems and operations, resilience cannot be claimed or measured. Compliance checks and system demonstrations show capability; they do not demonstrate operational resilience.
Measurement evaluates whether protection actually improves across ordered layers under real operating conditions—not controlled tests. Without measurable improvement, maturity cannot be assumed, and investment cannot be justified.
Measurement turns security from assumption into evidence.
Cumulative Defense Strategy excerpt from ASCE 78-24
Application
Architecture Responds to Gaps That Measurement Exposes
Security architecture is modified where performance fails to improve across defense layers protecting the perimeter, building envelope, interior pathways, and near-asset environments.
Measurement identifies exactly where layers are insufficient, misaligned, or redundant—allowing investment to be applied only where it produces measurable risk reduction. This approach replaces technology-driven deployments with outcome-driven design, while maintaining cost optimization. Cost-to-benefit calculations are part of the measurable outcome.